Trusted by 9,500+ global brands and organizations



MAXIMIZE TECH ROI
Optimize technology investments and ensure compliance
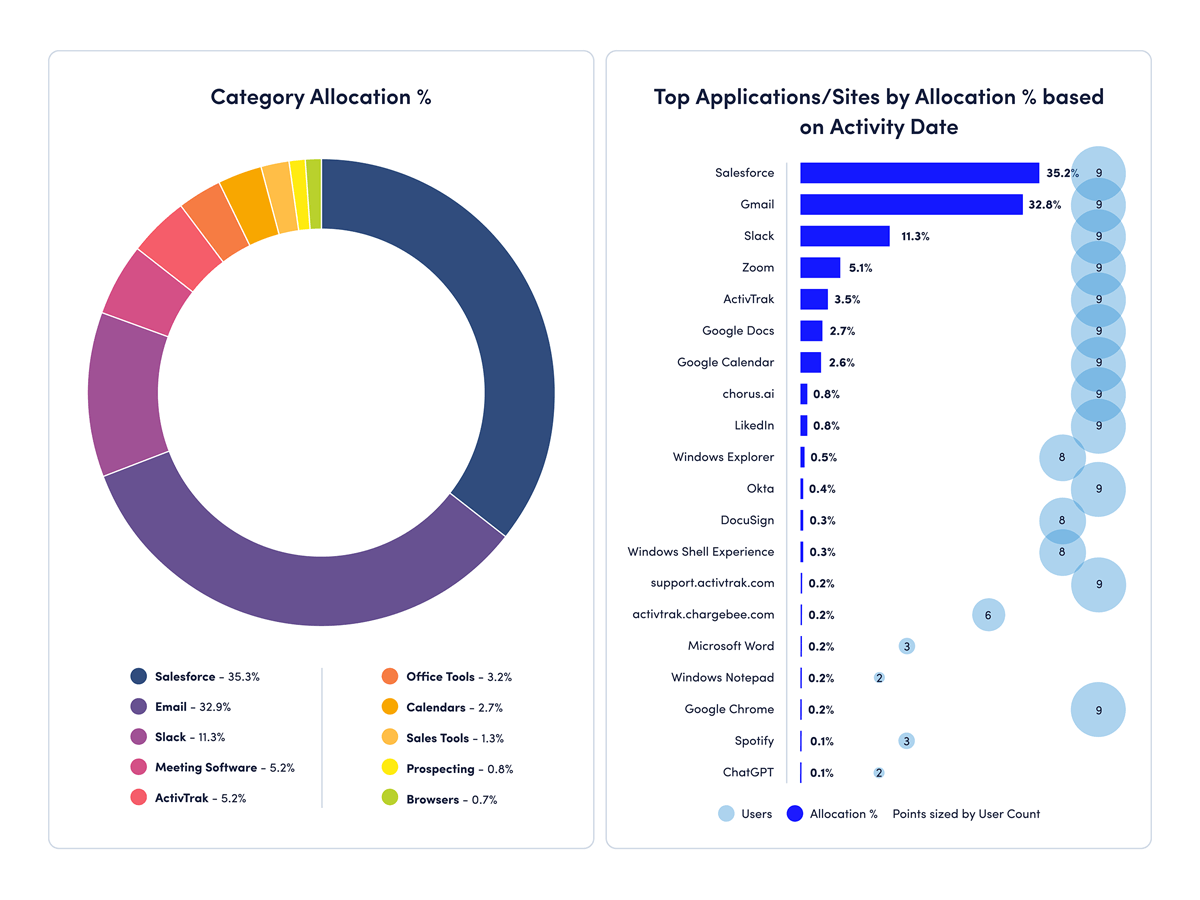
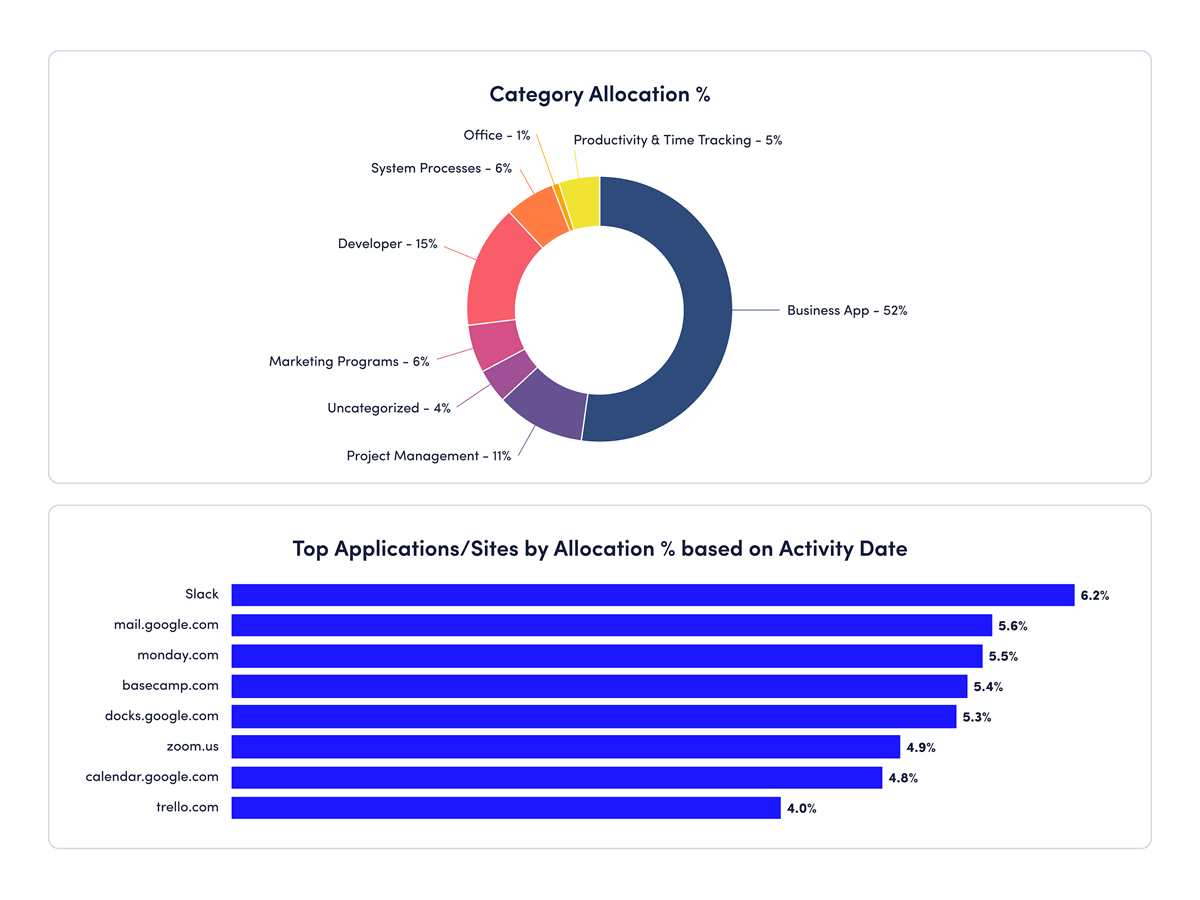
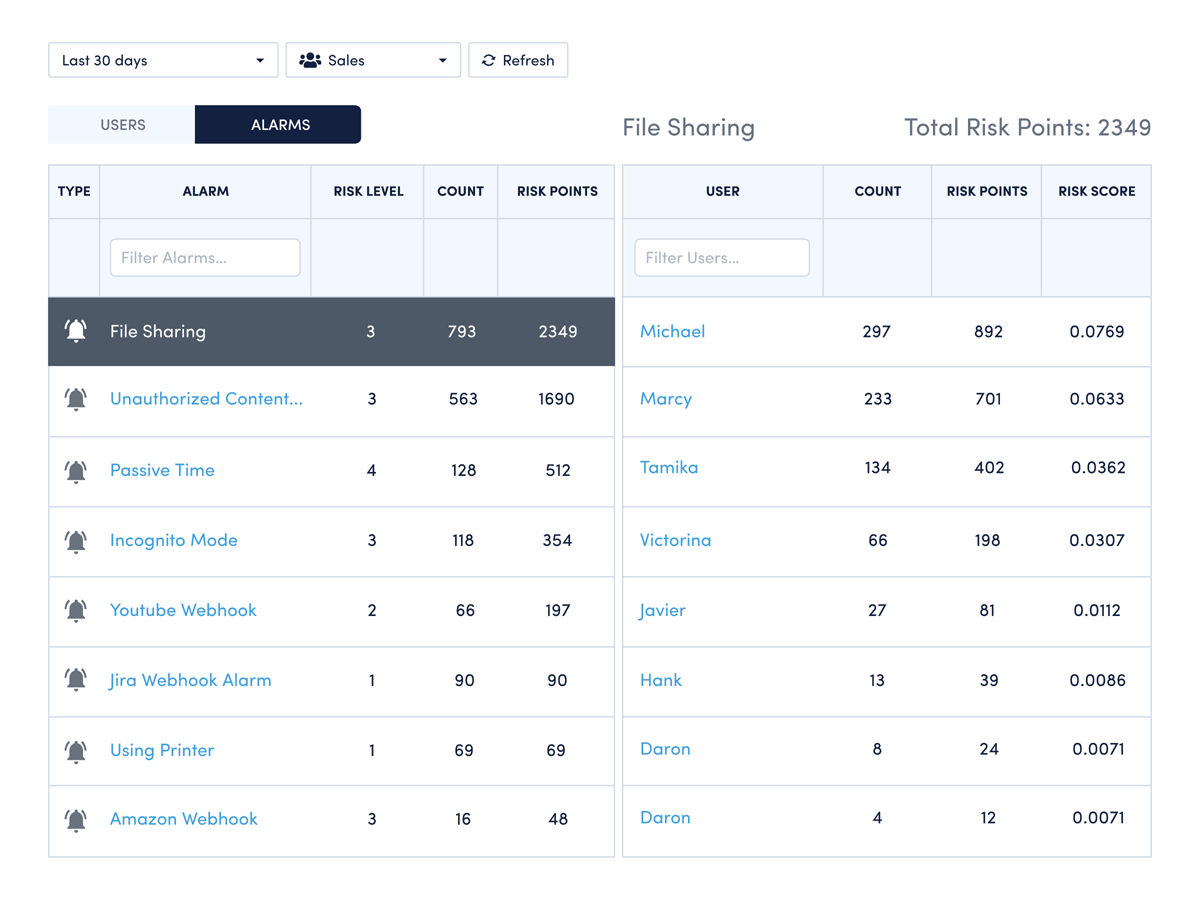
Understand where tools deliver value, cut costs from underused licenses and strengthen compliance through proactive monitoring.
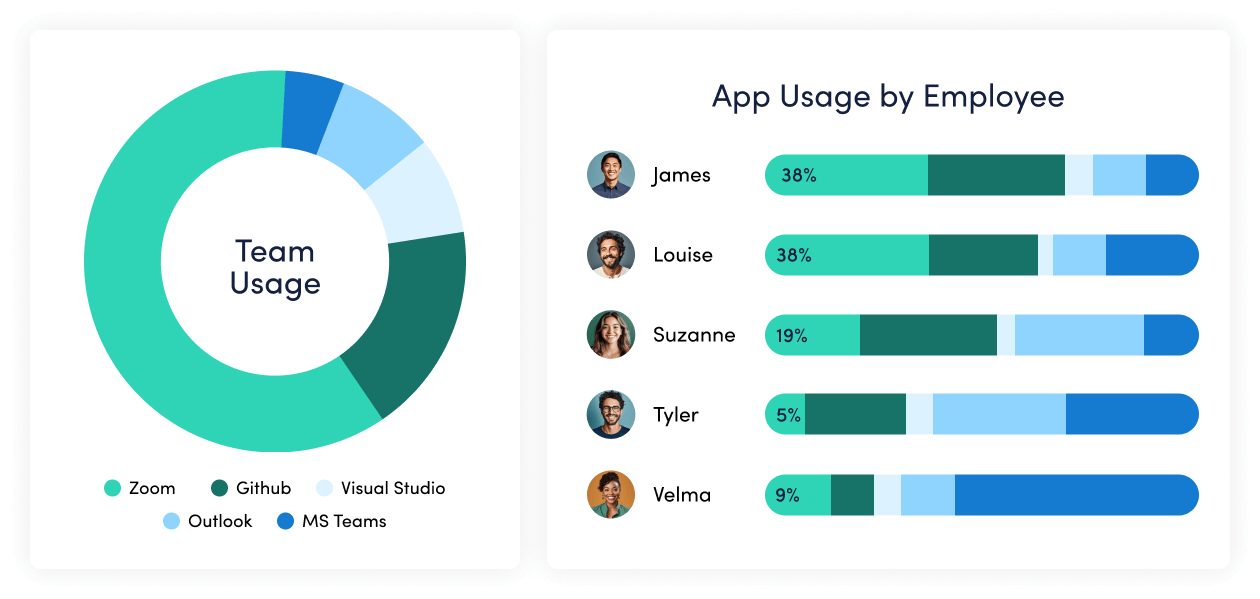
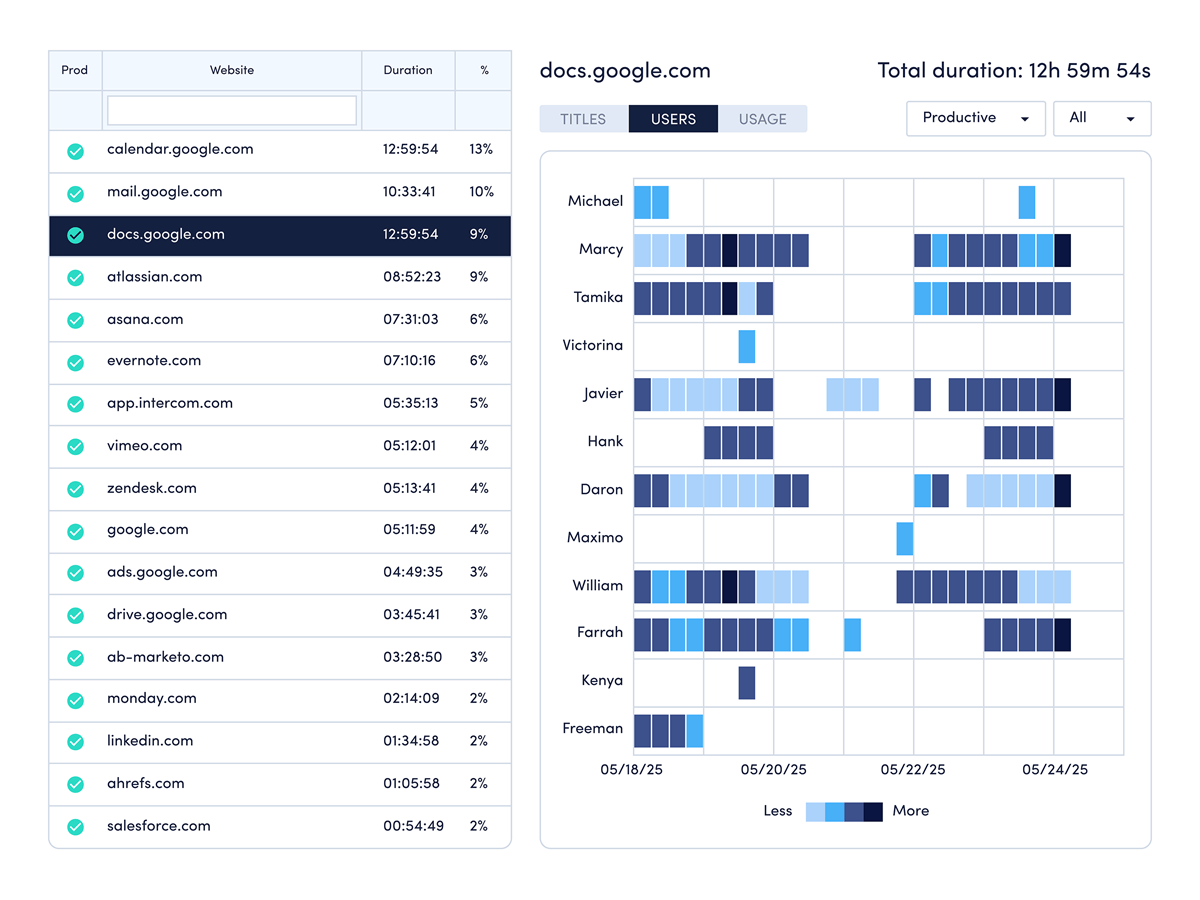
- Track technology adoption to maximize ROI
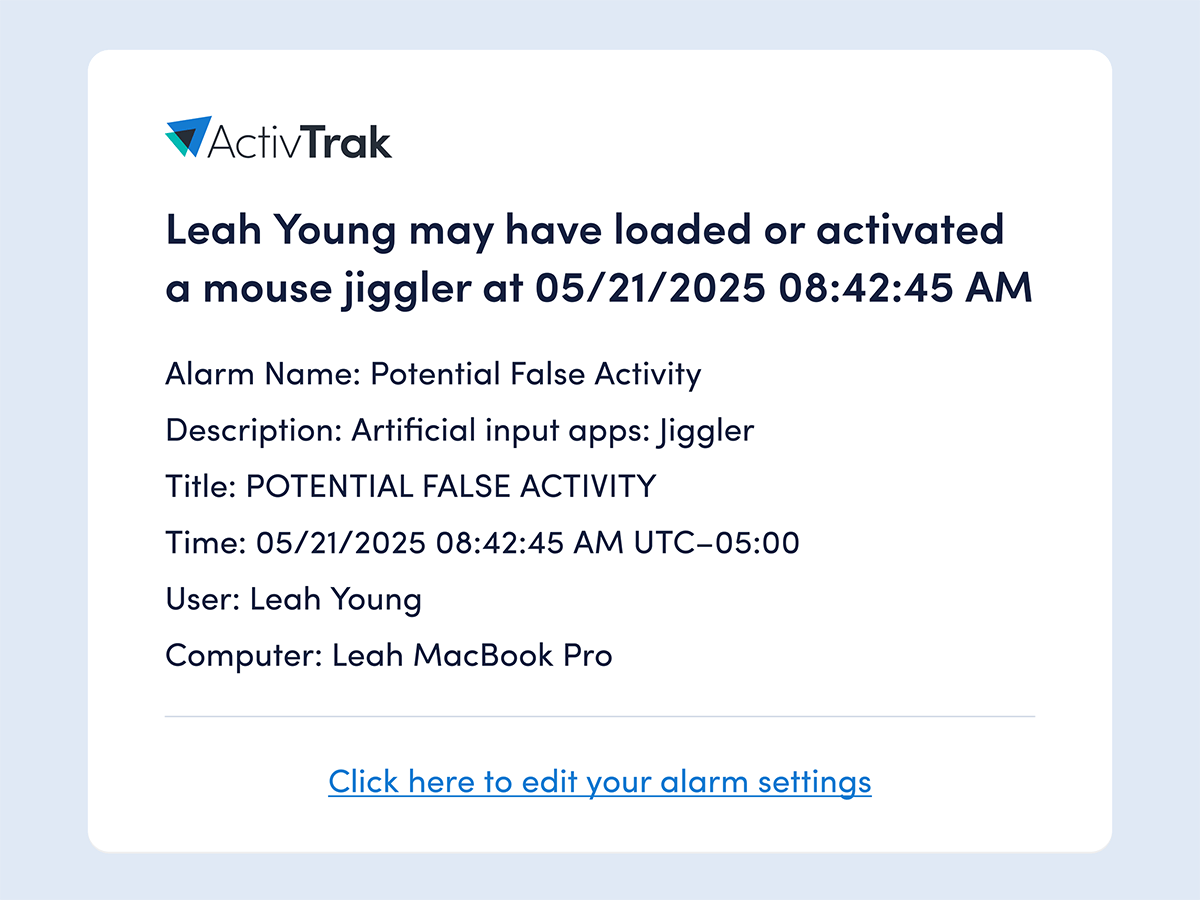
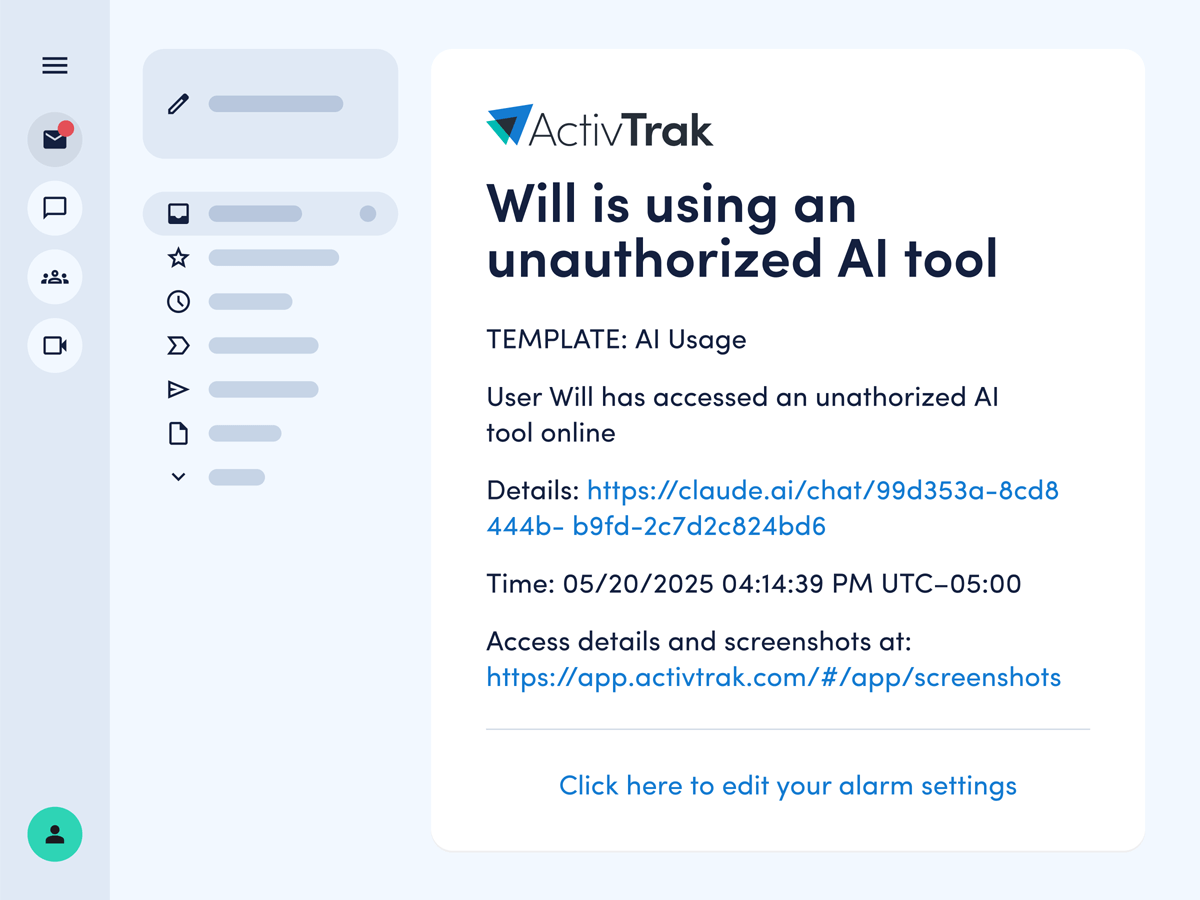
- Detect mouse jiggler and work simulation tools
- Identify individuals with repeat policy violations
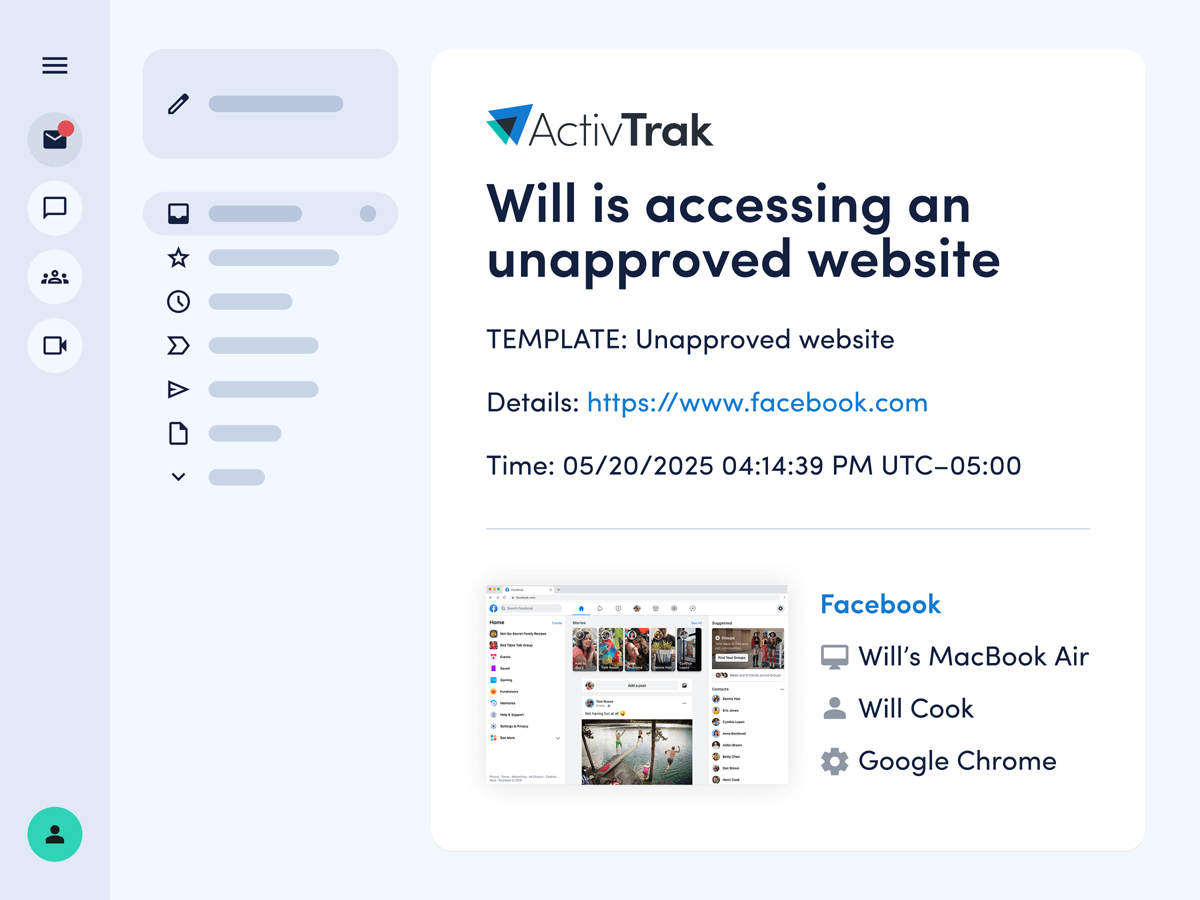
- Capture visual proof for compliance verification
- Take immediate action to prevent policy violations

ActivTrak alerts us of extended time spent on non-productive websites and inactivity. This has given us that information needed to reward productive staff and help others focus on business priorities.
— Director, R&D
INTERVENTION & PREVENTION
Act quickly to prevent policy violations
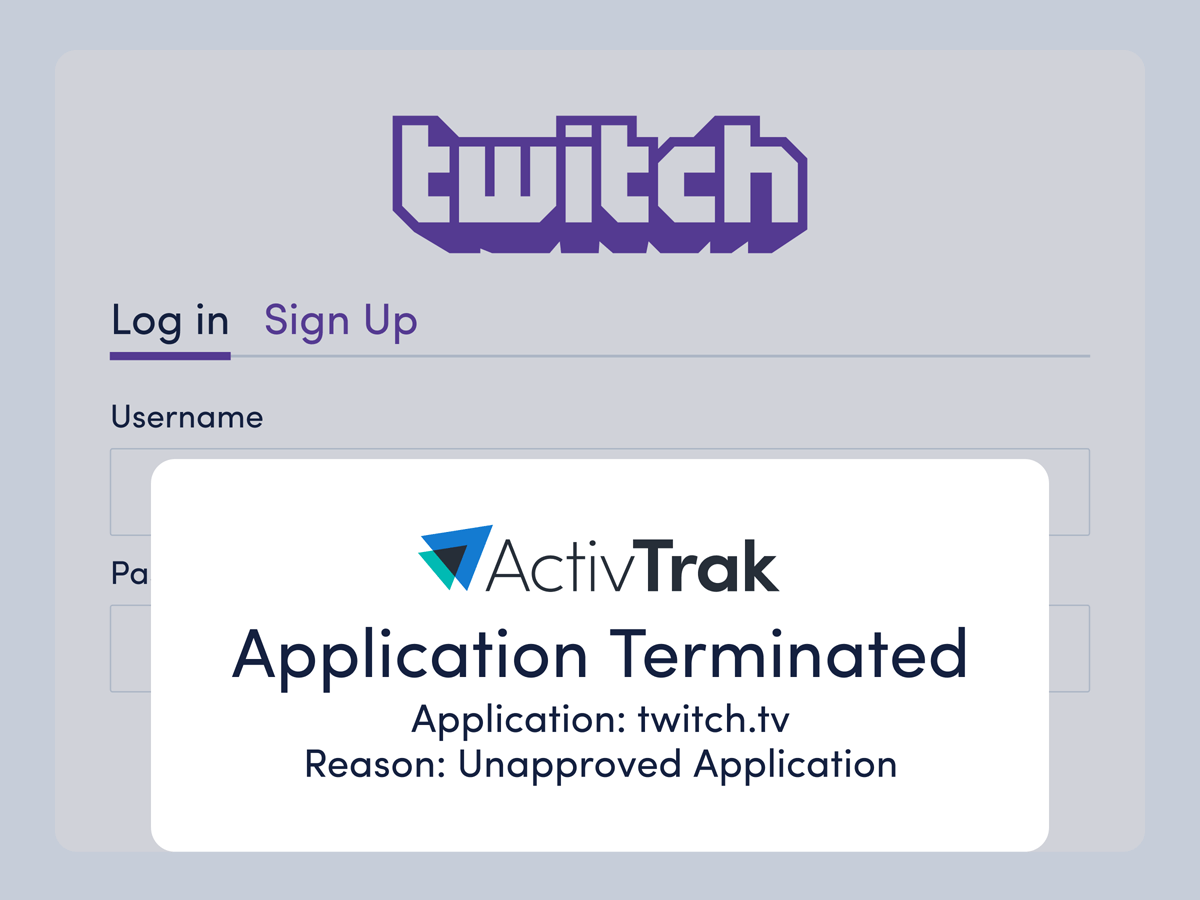
Application Termination
Automatically close unauthorized applications to maintain security compliance and prevent policy violations.
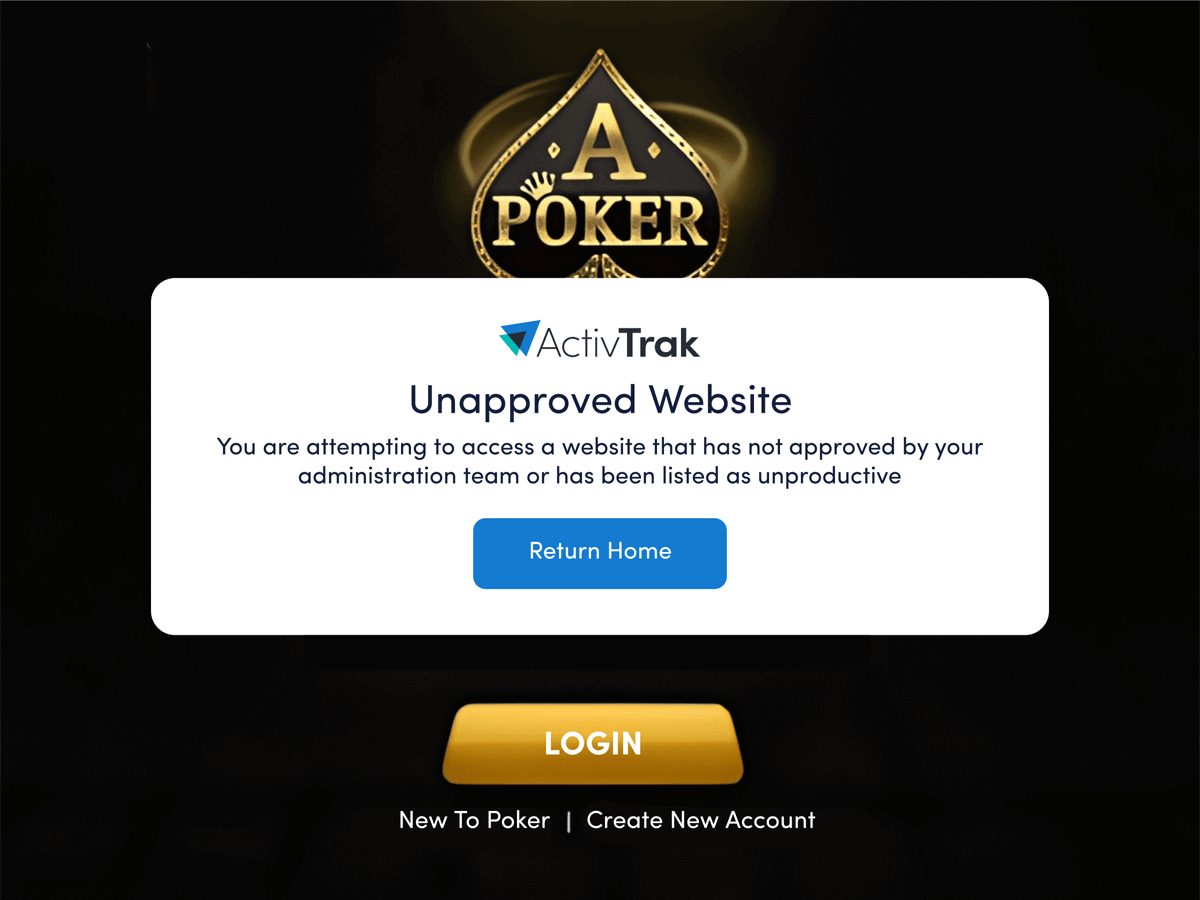
Pop Up Alarms
Display immediate on-screen notifications when policy violations are detected to prompt self-correction.
Connect work intelligence across your tech stack
Integrate existing tools to combine workforce activity, AI usage and business data for deeper, more actionable insights.

Workday

ADP
Microsoft Teams

Outlook

Google Calendar

ServiceNow

Zendesk
ChatGPT

Claude
Gemini
Microsoft Viva
Jira Software

Salesforce
Slack
How It Works
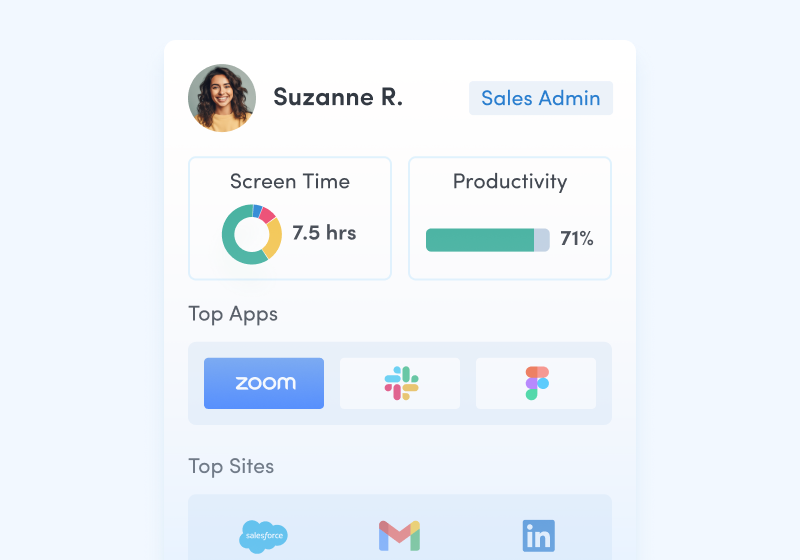
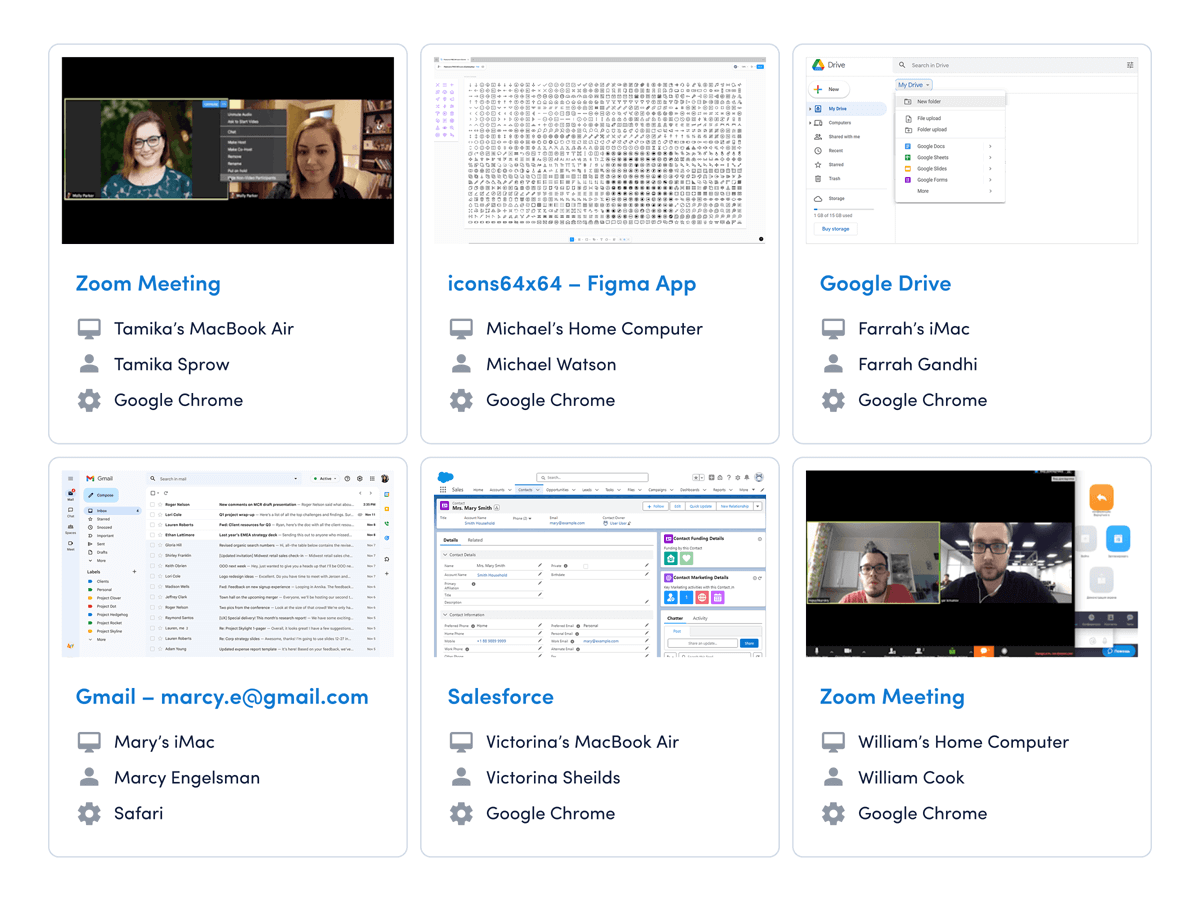
Capture behavioral activity
Capture behavioral activity including hours worked, schedule adherence, location policy compliance and app & website usage.

Analyze productivity trends
Analyze productivity trends on employee focus, engagement and utilization to make data-informed decisions on resource allocation.

Optimize team performance
Optimize team performance with benchmarks, goal-tracking and AI coaching recommendations to improve workforce productivity.
Getting started is easy.
Be up and running in minutes.