The key to achieving compliance is having complete visibility into every activity performed by a user that has access to personal data. Activities may include applications used (including cloud apps), websites visited, records copied, and files saved. Clear visibility into and monitoring of this behavior lets you truly understand how sensitive data is accessed, shared and/or misused across your organization.
During this 45-minute product training, we will show you how to leverage ActivTrak to:
- Continuously monitor the applications and processes to ensure policy alignment
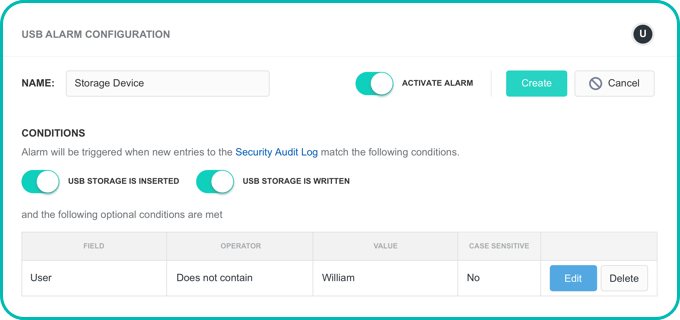
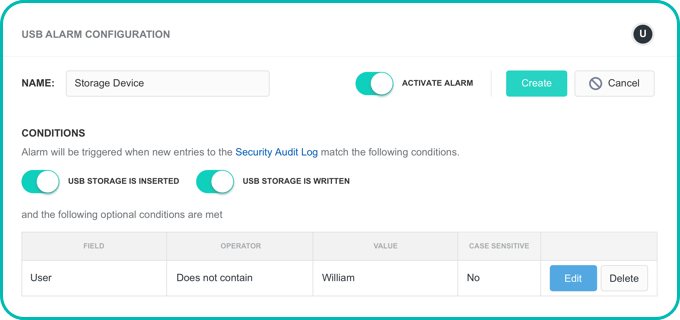
- Set customizable alerts to pinpoint high-risk user activities that compromise sensitive data
- Assess risk and ensure safeguards are in place
- How to respond in the event a data breach occurs
- Instantly generate compliance reports to document audit trails